What Is a Nonce in Security? Definition, Uses, and Importance Explained
A nonce in security is a unique, one-time-use number—usually random or pseudo-random—that ensures freshness and prevents replay attacks in cryptographic communications. It’s central to keeping sessions secure, whether you’re authorizing a login, encrypting data, or mining a blockchain.
Why a Nonce Matters
A nonce isn’t just a random number tossed in for fun—it’s a critical safeguard. It ensures that the same message or request can’t be resent maliciously. Without it, attackers can intercept and replay old communications and trick systems into acting again on your behalf. This concept is used everywhere from logging in, to encryption, even to issuing blockchain tokens.
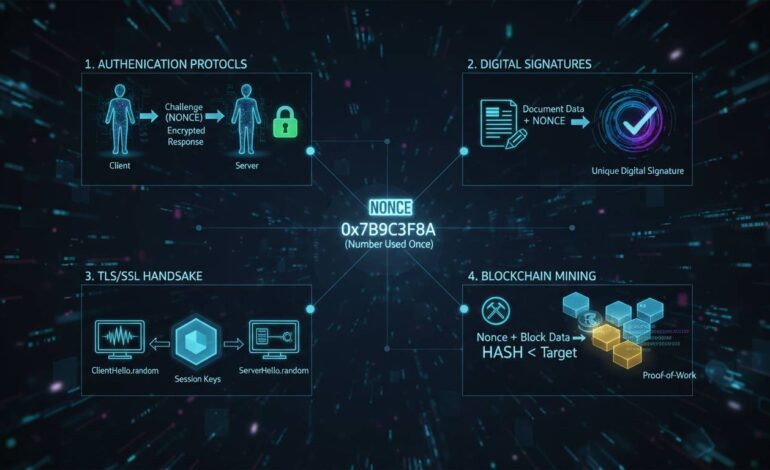
How Nonces Work Across Different Scenarios
Authentication Protocols: Keeping Things Fresh
During login or challenge-response systems, servers generate a nonce and send it to the client. The client uses it to compute a response—if the nonce is wrong or reused, the server rejects the request. This thwarts repeat attacks. Many widely used protocols, like HTTP Digest Authentication, rely on this principle.
Encryption: Adding Uniqueness to Ciphertext
Nonces act like initialization vectors (IVs) in encryption. Even if you encrypt the same message twice with the same key, a different nonce will produce a different result—making it harder to analyze patterns. AES-GCM and ChaCha20-Poly1305 are common encryption schemes that depend on this. They’re vital for data integrity and confidentiality, especially when large volumes of similar data are transmitted.
Blockchain: Proof-of-Work and Transaction Integrity
In blockchain systems like Bitcoin, a nonce is a variable that miners adjust in the block header to meet the hash difficulty target. This trial-and-error process secures the network through Proof-of-Work. Without the right nonce, miners can’t produce a valid block—this underpins the trustless system.
Smart contract platforms also use transaction nonces to track order and prevent replayed transactions—each action increments the nonce.
Types of Nonce Generation
-
Random Nonce
Generated via a secure algorithm. Offers strong unpredictability but needs enough randomness to avoid collisions. -
Sequential Nonce
Incremental and predictable. Good for tracking, but weak on randomness and security. -
Hybrid or Combined
Leverages both randomness and sequence. Offers a decent balance—like adding a timestamp to a random base.
Nonce quality matters: poor randomness or reused values can undermine entire protocols.
Real-World Examples That Hit Home
-
Payment Processing
Imagine placing an online order. If the same request were reused, a malicious actor could replay it for duplicate charges. A nonce blocks that. -
CAPTCHAs and OTPs
These are simple forms of nonces—used only once, expire quickly, and validate a specific human or transaction request. -
Stream Ciphers
When encrypting multiple messages with the same key, using a new nonce each time ensures ciphertext stays unique. -
ECDSA Signatures
A cryptographic case: leaking even part of the nonce used in ECDSA can reveal the private key. A recent study exposed how sleep-induced power fluctuations might leak 20 bits of a nonce—showing even small quirks can compromise security.
Risks When Nonces Aren’t Handled Right
-
Nonce Collisions or Reuse
Reusing a nonce with the same key breaks encryption schemes—enabling attacks and pattern detection. -
Poor Randomness
Predictable nonces let attackers precompute or guess values—defeating protections. -
Side-Channel Attacks
As with that ECDSA study—nonces can leak through hardware characteristics, not just code. -
Replay Sessions
Without unique nonce handling, even standard auth flows can be hijacked through replay.
Best Practices for Nonce Use
- Always generate fresh nonces—never reuse them, especially with the same key.
- Prefer cryptographically secure random generation methods.
- For sequential nonces, combine with randomness or timestamps to confuse attackers.
- Handling and storage should ensure they’re used only once and then discarded.
- Watch for side-channel exposure in critical systems—like ECDSA.
“Nonce should be truly unique and unpredictable. Without that, even the best crypto can fail.”
Adhering to these guidelines keeps systems robust and trusted.
Conclusion
Nonce—simple to define, but indispensable in security. Whether authenticating users, encrypting data, or securing blockchains, nonces ensure freshness, uniqueness, and trust. Implemented well, they stop replay attacks, enforce integrity, and make cryptographic systems reliable. Messed up? Even tiny nonce errors can spell disaster, from leaking keys to exposing user data. Design thoughtfully, randomize well, and handle nonces with care—and your security stands much stronger.
FAQs
What exactly does nonce stand for?
It loosely means “number used once”—a unique identifier intended for one-time use, often random or timestamped.
How do nonces stop replay attacks?
Each message uses a new, valid-only-once value. Any resubmission with the same nonce gets rejected—so replayed requests are useless.
Why is randomness essential in nonces?
Predictable nonces let attackers guess or reuse them. Randomness ensures nonces are unguessable and secure.
Can nonces be reused safely?
No. Reuse is insecure, especially in encryption. Every crypto operation needs a new nonce to remain safe.
Do all protocols use nonces?
Most security protocols—authentication, encryption, blockchain protocols, digital signatures—use nonces in some form to ensure integrity and freshness.